top of page


AI Agents & Cybersecurity
Article written by: Neel Ramachandran What is an AI Agent? An AI Agent is a software program that can observe its environment, make decisions based on those observations, and take actions to achieve a specific objective. Unlike traditional software that follows rigid, pre-programmed rules, AI agents are adaptive. They can learn from new data, adjust their strategies over time, and operate with a degree of independence. In cybersecurity, the “environment” an AI agent observes

Neel Ramachandran
May 302 min read


Important Cryptography Techniques to Know
Article Written By: Lakkshanasre Viyasarramnujam Article Designed by: Lakkshanasre Viyasarramnujam and Natasha Gumpula Important Cryptography Techniques to Know ______________________________________________________________ In the world of intricate security, one thing remains crucial: the power of cryptography. It's the clever work of techniques and methods that ensure that we can keep our systems and exchange of information private from attackers. So if you’re curious about

Lakkshanasre Viyasarramanujam
May 293 min read

Case-Study of the MGM & Caesars Cyberattack
Article Written By: Lakkshanasre Viyasarramanujam Article Designed by: Lakkshanasre Viyasarramanujam & Sanvi Desai The Target and the Players In September 2023, the city of Las Vegas broke down, from its glitz and glamorous fortunes to becoming the stage for one of the most significant and public cyberattacks, and it affected the two titans in Las Vegas’s best of the hospitality industry: MGM Resorts International and Caesars Entertainment. Behind this clever digital heist w

Lakkshanasre Viyasarramanujam
May 23 min read


Social Engineering
AttacksHacking humans instead of systems Article Written By: Iyithihya Prakasan Article Designed by: Iyithihya Prakasan and Natasha Gumpula What is Social Engineering? Social engineering (IBM) attacks work their way to orchestrate individuals to part with information that they are not supposed to share, install software that they are not supposed to install, open web pages that they are not supposed to visit, send money to criminals, or commit other errors that jeopardize the

Iyithihya Prakasan
May 13 min read


AI-Facilitated Research: Pros & Cons
Article Written By: Jia Fletcher Article Designed by: Jia Fletcher & Sanvi Desai The Rise of AI-Facilitated Research In our digital world, it has become increasingly common for artificial intelligence to be used as a tool to improve our daily lives. For students, AI is making its way into research. AI-facilitated research involves the integration of artificial intelligence in the research process. This is starting to be seen more commonly in schools.

Jia Fletcher
Apr 152 min read


Cybersecurity Requirements for Remote Operations (6G & Tele-surgery)
Protection of Patients Safety and Data Integrity in Next-Generation Medical Netw Article Written By: Iyithihya Prakasan Article Designed by: Iyithihya Prakasan and Natasha Gumpula With the technological development of remote surgery , a physician can soon remotely control robotic tools with super-speedy networks such as 6G . To ensure this works safely, then we can use good cybersecurity to ensure protection of patients, doctors and the complete system at large. Image from

Iyithihya Prakasan
Apr 93 min read


A Comprehensive Analysis of Quantum Computing: Engineering Challenges and Opportunities
Article Written By: Adrian Bermudez Article Designed by: Adrian Bermudez & Sanvi Desai Quantum computing is seen as the imminent revolution in computational science; this comes after the challenges to the foundational paradigms of classical physics and information theory. Quantum computing is promising the ability to tackle problems deemed insurmountable by even the most powerful conventional supercomputers. Unlike classical computers that process bits as either 0 or 1, quan
Adrian Bermudez
Mar 295 min read


Important Cybersecurity Techniques to Know
Article Written By: Lakkshanasre Viyasarramanujam Article Designed by: Natasha Gumpula and Lakkshanasre Viyasarramanujam In the world of intricate security, one thing remains crucial: the power of cryptography. It's the clever work of techniques and methods that ensure that we can keep our systems and exchange of information private from attackers. So if you’re curious about learning how these digital locks work, we will learn about the importance of cryptography and the diff

Lakkshanasre Viyasarramanujam
Mar 263 min read


FUHSD Board Approves Policy Changes
Article Written By: Sanvi Desai & Natasha Gumpula For many students in the Fremont Union High School District (FUHSD), cyberbullying has been something people quietly deal with rather than something schools actively address. That’s what made the FUHSD Board of Trustees meeting on February 10, 2026 feel different. Students showed up, not just in person, but online too, to support a push for stronger aftermath protections. Members of Cyber For Youth and student advocates Sa

Sanvi Desai
Mar 222 min read
Deepfake Texts and Voices: The New Risk to Employers
Article written by: Chintana Bhaskara Article designed by: Chintana Bhaskara & Sanvi Desai Deepfake Texts and Voices: The New Risk to Employers AI Deepfake Voices Cybercriminals are now creating AI-generated voices and videos to sound like real people. These deepfake voices trick employees into sharing sensitive data, money, or files, to their supposed “boss.” Attackers use old emails, texts, or videos to make their message sound more realistic and believable. In addition, c

Chintana Bhaskara
Mar 162 min read


Engineering and Cybersecurity Ethics in the Age of AI
Article written by: Adrian Bermudez Article designed by: Adrian Bermudez and Natasha Gumpula The Engineering Foundations of AI Systems Twenty-first century artificial intelligence (AI) systems hinge on complex engineering infrastructures that combine large-scale data processing, machine learning algorithms, and specialized computing hardware. The development of modern AI typically follows a structured pipeline, including data collection, preprocessing, model training, validat
Adrian Bermudez
Mar 134 min read


How is AI affecting the environment?
Article written by: Sanika Lovlekar Article designed by: Sanika Lovlekar & Sanvi Desai Introduction A common topic which is generally brought up during practical conversations is “ Will AI take over the world and will it replace human jobs? ” Whether the answer to this question is yes or no, AI surely damages our planet. Even if AI doesn’t replace every single job in the world, if we continue to misuse it, the condition of Earth’s natural environment will decay. Over time, a
Sanika Lovlekar
Mar 103 min read


Quantum Computing and What It Means for Encryption
Article Written by: Rishi Ramachandran Article Des igned by: Rishi Ramachandran and Natasha Gumpula You may have heard the phrase quantum computing tossed around and wondered what it actually means, and more importantly, why people in cybersecurity care so much about it all of a sudden. The short answer is that quantum computing has the potential to change how computers solve problems, and in doing so, it could break the encryption systems that protect almost everything we d
Rishi Ramachandran
Mar 73 min read


What are Cookies?
Article Written by: Jia Fletcher Article Des igned by: Jia Fletcher & Sanvi Desai (Image from myonlinemarketing.ch ) Not Your Regular Cookie Do you know what cookies are? No—I’m not talking about the delectable, chocolatey desserts you’re now suddenly craving. I’m talking about web cookies . Does that ring a bell? Most times when you open a new website, you may see a popup that asks you to either “accept all cookies” or adjust your cookie preferences. What exactly are these

Jia Fletcher
Feb 273 min read


The Dark Side of QR Codes: How a Simple Convenience Became a Risk
Article Written by: Chintana Bhaskara Article Designed by: Chintana Bhaskara and Natasha Gumpula A Convenience Turned Into a Trap One scan is all it takes. A quick snap on your phone camera of a QR code at a public parking lot, in an email, on a poster, and now you’ve just given hackers all your personal data. Something that was created for the convenience of people has become one of the easiest traps that people fall into all the time. QR codes were built for the convenience

Chintana Bhaskara
Feb 243 min read


Recent Russian hacks on Dutch public infrastructure
Article Written by: Aryan Singh Article Designed by: Aryan Singh & Sanvi Desai What comes to mind when you hear the word “cyberattack”? When people think of cyberattacks, they usually think of attackers targeting computers and websites. But that is quickly changing. Today, cyberattacks are hitting physical infrastructure we rely on every day. Since these systems are run by computers, they are increasingly becoming new targets for hackers. A recent example of this happened in
Aryan Singh
Feb 183 min read


Thinking Like An Attacker: How Social Engineering Works
Article Written by: Avni Sharma Article Designed by: Avni Sharma and Natasha Gumpula Phishing is one of the most common forms of cyberattacks today, and it often sounds surprisingly realistic. Attackers craft emails or messages that look legitimate, convincing victims to click links, share sensitive information, or even transfer money. This is part of a broader strategy known as social engineering, where criminals use psychological tactics to gain trust and manipulate people
Avni Sharma
Feb 172 min read


Nvidia and OpenAI: An Alliance for the Future
Article Written by: Jia Fletcher Article Designed by: Jia Fletcher & Sanvi Desai Over 90% of leading businesses utilize AI. Artificial intelligence has become a prominent force in our everyday lives, making its way into businesses and homes alike. Now, two leading companies in the artificial intelligence industry– Nvidia and OpenAI –have just made history. On September 22, 2025 , Nvidia and OpenAI publicly announced their partnership. The two companies both have significant

Jia Fletcher
Feb 113 min read


The Hidden Life of Your Data: What Apps Really do Behind the Scenes
Article Written By: Chintana Bhaskara Article Designed By: Chintana Bhaskara and Natasha Gumpula Hidden Data Flow A study shows that of the 297 popular health and fitness apps , found that there are about 8 different permissions asked, including sensitive information like your location or device information. Even though most apps state that they don’t share your data with outside sources, it has shown to be untrue. Grund, Held & Bero states that researchers have discovered t

Chintana Bhaskara
Feb 103 min read

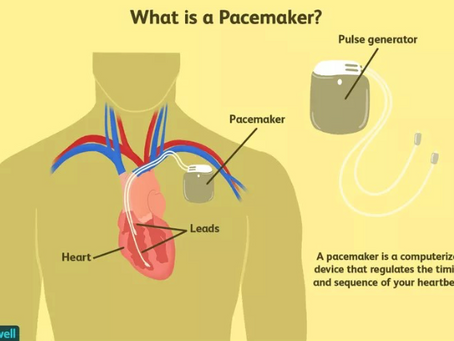
Cyber Security for Cardiac Devices
Article Written By: Iyithihya Prakasan Article Designed By: Iyithihya Prakasan & Sanvi Desai Ever wondered about the possibilities of a pacemaker being a threat? What is the purpose of a pacemaker in the human body? A pacemaker is a device that helps you regulate the timing and sequence of your heartbeat. It cannot exactly replace your heart but can help regulate your heartbeat artificially. Image from verywell health Functioning of pacemakers Once installed, the pacemaker

Iyithihya Prakasan
Feb 53 min read
bottom of page
