Cyber Security for Cardiac Devices
- Iyithihya Prakasan

- Feb 5
- 3 min read
Article Written By: Iyithihya Prakasan
Article Designed By: Iyithihya Prakasan & Sanvi Desai
Ever wondered about the possibilities of a pacemaker being a threat?

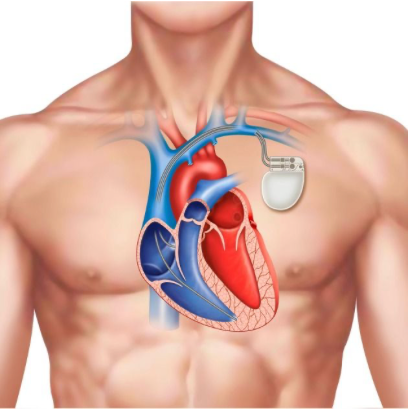
What is the purpose of a pacemaker in the human body?
A pacemaker is a device that helps you regulate the timing and sequence of your heartbeat. It cannot exactly replace your heart but can help regulate your heartbeat artificially.
Image from verywell health
Functioning of pacemakers
Once installed, the pacemaker monitors your heart's activity and if your heart rate is low, the device will kick in and send an electrical signal to the heart muscle to contract.
Cardiac devices (CIED) like pacemakers, ICD, and cardiac loop recorders are implantable electronic devices designed to help control or monitor irregular heartbeats in people with heart failure and certain heart rhythm disorders.

Concerns and threats that may arise upon these devices; importance of Cyber Security.
CIED’s recent advancements in cardiac technology allows the transmission and interrogation which invades into the data of these devices and lets the hacker monitor/control the device.
Image from Buzzfeed
The importance of cyber security is evident when the hacker misuses the connection, taking advantage of the weak security and starts controlling the device which could turn fatal in the worst scenario.
Remote monitoring of pacemakers involves transmission of data from the patient's device to healthcare professionals.

The data includes the functioning of the device on the patient's body, the cardiovascular events, the patient’s clinical status and even technical information about the hospital. These information is analysed by medical professionals to curate custom medications, tailor therapy and even reprogram the device if necessary.
Image from Vecteezy
Is reprogramming a gateway into intrusion for a hacker?

In the current status of CIEDs,the reprogramming of the device isn’t possible remotely; and for any reprogramming, it is required for the patient to provide an in-person visit to the hospital of installation.
Remote monitoring was a game changer as it helped reduce frequent hospitalizations and improved survival with patient outcomes. It overall reduced the cost burden and strain on health care providers,therefore remote monitoring is highly promoted.
Image from Pinterest
How do hackers target and implement their purpose on cardiac devices?
Cardiac access can occur wirelessly through radio frequency, bluetooth technology or even smart phones. It can deliver unnatural shocks, kill the battery, halt the monitoring and interrupt the therapy of the patient. CIEDs can also be hacked to gain access to the hospital’s computer network and data.
CIED-Monitor/Programmer communication interception: Using software-defined radio (SDR) to intercept the RF signals.
Accessing the device USB port and reading or extraction of the monitor files.
Insertion of a backdoor (malware) into the monitor to modify/erase the contents of the monitor memory or induce programmer reading errors or cause spoof programming.
Initiate boundless telemetry sessions: maintain a telemetry session indefinitely active by regularly sending commands to prematurely reduce the CIED's battery lifetime.
Accessing the CIED ecosystem during firmware updates or levering into the device's local network access to interfere with the communication between the programmer and software update provider.
How manufacturing technology could possibly prevent and protect cardiac devices
We can protect the cardiac device by using advanced materials and implementing manufacturing techniques such as 3D printing and fabrications. CIEDs are vital in healthcare but can also be fatal due to our negligence. Cyber security for CIEDS is a crucial matter and therefore requires timely collaboration with the device manufacturer, physicians, governmental regulatory body, IT specialists and the patient.
The process for cybersecurity through the conception and design of CIEDs
Once implanted, the post-implant surveillance must be the responsibility of the doctors and manufacturers to identify vulnerabilities and address these issues quickly so that the device can be curated in a custom manner considering the patient's health and do so throughout the lifespan of CIEDs.
Patients' data should always be encrypted and transferred via a secure network.
A high level of security in data transmission must be employed using principles of confidentiality, integrity, authenticity, accountability, and reliability.
CIED access to hackers should be prevented and rarely the remote monitoring option may have to be temporarily disabled.
Image from Ginger Health
Works Cited
Kapoor, Aditya, et al. “Cardiac devices and cyber attacks: How far are they real? How to overcome?” Science Direct, National Library of Medicine, Pub. Med Central. Accessed 23 November 2025.
Fogoros, Richard N. “How Does a Pacemaker Work?” Verywell Health, 16 October 2025,verywell health. Accessed 23 November 2025.
Cingolani, et al. “Next-generation pacemakers: from small devices to biological pacemakers.” Nature, 16 November 2017,Nature. Accessed 24 November 2024.
Parsonnet, Victor, et al. “Pacemaker-implantation complication rates: An analysis of some contributing factors.” Science Direct, Journal of the American College of Cardiology, 13 February 2004 Journal of the American College of Cardiology,. Accessed 25 November 2025.



Damn you ate that up